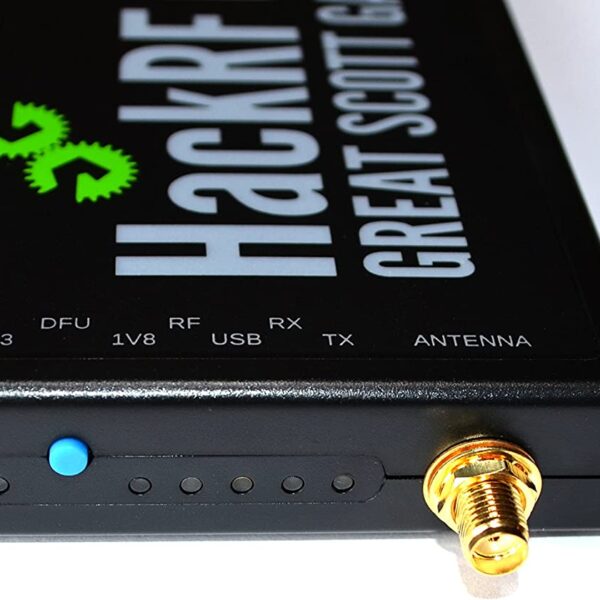
HackRF One: Introduction to the HackRF One
A Revolution in Software-Defined Radio (SDR) Journey through the evolution of software-defined radio with the HackRF One. This groundbreaking creation has redefined the possibilities of wireless communication. In this exploration, we uncover the history, the ingenious mind behind it, and the myriad of applications that make the HackRF One a game-changer.The Genesis of HackRF One:Conceived by the brilliant mind of Michael Ossmann. The HackRF has emerged as an open-source SDR platform. It's designed to empower enthusiasts, hackers, and researchers alike.…